Search K
Appearance
Appearance
Released: 2025-07-17
The Exim mail server configuration is extended to block user attempts to spoof the sender address. This is implemented as an additional Exim ACL for email submitted over SMTP. The ACL checks the username from the SMTP authentication against the sender address provided in the SMTP MAIL FROM command (also known as the envelope sender).
The general idea of sender address validation is to allow an email account to be able to send from any address as long as an email reply to the sender address would be routed back to the same email account.
Valid sender address examples:
The sender address spoofing protection is enabled by default. However, it can be explicitly disabled to stay backwards compatible with the old Exim configuration by setting the AUTH_BLOCK_SENDER_SPOOFING = no variable in the /etc/exim.variables.conf.custom file.
# Disable sender address validation (insecure):
sed -i '/^AUTH_BLOCK_SENDER_SPOOFING /d' /etc/exim.variables.conf.custom
echo 'AUTH_BLOCK_SENDER_SPOOFING = no' >> /etc/exim.variables.conf.custom
da build exim_conf
# Restore sender address validation:
sed -i '/^AUTH_BLOCK_SENDER_SPOOFING /d' /etc/exim.variables.conf.custom
da build exim_confThere may be cases where you want to allow a given smtp-authenticatedd User/E-Mail to bypass these rules. Similar to the above guide to disable the feature entirely, instead of using no as the value, we'll use whitelist lookkup file. Add this to your /etc/exim.variables.conf.custom:
AUTH_BLOCK_SENDER_SPOOFING = ${lookup{$authenticated_id}lsearch{/etc/virtual/whitelist_sender_spoofing_auth}{no}{yes}}and build the exim.conf:
da build exim_confAdd any email@address.com value to the /etc/virtual/whitelist_sender_spoofing_auth file, one value per line.
This method of specifying exim code the AUTH_BLOCK_SENDER_SPOOFING variable could be used to block/allow things with any other logic that you wish to use (exim coding knowledge required)
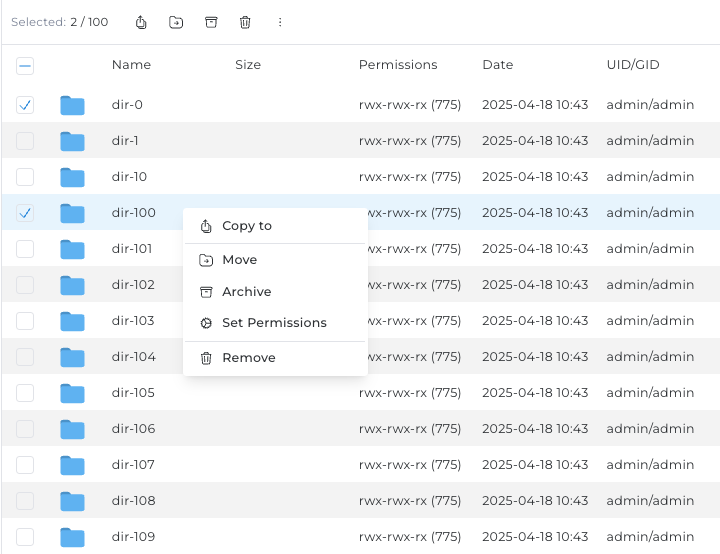
The File Manager's files and folders table has been redesigned with a new design and optimized rendering logic, resulting in improved performance and a more streamlined user experience when browsing and managing files.
The layout is kept the same, ensuring that users can continue to navigate and interact with the File Manager as before.
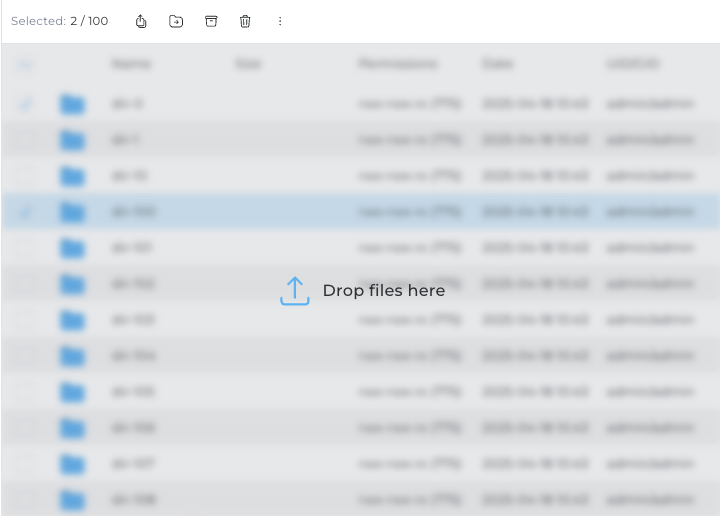
The drag and drop functionality in the File Manager has been reworked for greater reliability and usability. Files and folders can now only be dropped onto the main files and folders table area, which immediately triggers the upload dialog for the dropped items. This change eliminates previous bugs and ensures a more consistent and predictable upload experience.
apache2.4 updated from 2.4.63 to 2.4.65composer updated from 2.8.9 to 2.8.10litespeed updated from 6.3.3-1 to 6.3.3-2lz4 (PHP extension) updated from 0.4.4 to 0.5.0modsecurity_owasp_rules updated from 4.15.0 to 4.16.0modsecurity updated from 2.9.10 to 2.9.11nginx updated from 1.28.0 to 1.29.0PHP 8.1 updated from 8.1.32 to 8.1.33PHP 8.2 updated from 8.2.28 to 8.2.29PHP 8.3 updated from 8.3.22 to 8.3.23PHP 8.4 updated from 8.4.8 to 8.4.10redis updated from 8.0.2 to 8.0.3Note:
Using apache2.4.64 together with nginx may require to enable passing of the server name through TLS Server Name Indication extension in nginx config when using ssl reverse proxy.
# Example for nginx_apache webserver
# When overriding Host header for SSL reverse proxy
proxy_pass https://example.com;
proxy_set_header Host $host;
proxy_ssl_name $host;
proxy_ssl_server_name on;See proxy_ssl_server_name and proxy_ssl_name.
Ticking the "Wildcard" option (found within admin level -> Account Manager -> SSL Certificates -> Get automatic certificate from ACME Provider) previously did not preselect the required certificate entry options.
cakey, cacert, carootcert configuration options from directadmin.conf removal The location of server host name TLS certificate files can no longer be customised. The files will always be stored in the default locations:
/usr/local/directadmin/conf/cakey.pem - server host name TLS key./usr/local/directadmin/conf/cacert.pem - server host name TLS certificate./usr/local/directadmin/conf/carootcert.pem - intermediate CA certificates.On the servers where these options were set to non-default values, the certificate files will be automatically copied to the default location.
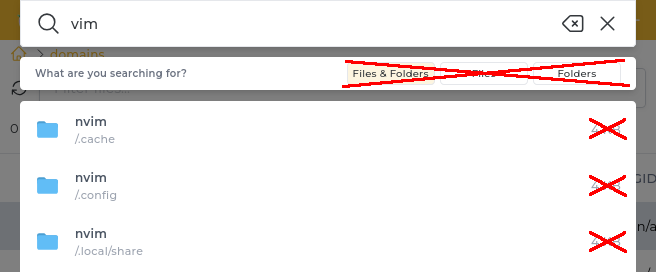
Simplified files search in filemanager.
/CMD_FILE_MANAGER?action=recursive_search changes:
type filterThe default IP apache vhost template is cleaned up by removing UserDir directives, previously used when userdir_access CB option, was enabled.
HAVE_USERDIR_ACCESS token is always 0
It is no longer possible to select how much space a menu category could take up.
The filtering feature of files and folders in the File Manager was removed.